
 VulpineOS
VulpineOS
Operate browser agents on a hardened Firefox runtime with real operator controls, remote access, and a clear split between the open-source stack and the commercial surfaces built on top of it.
What Ships Now
| Surface | What it is |
|---|---|
| VulpineOS | Public browser-agent runtime on Camoufox with agent orchestration, web panel, TUI, remote server, and MCP tools |
| Foxbridge | Public CDP-to-Firefox bridge for OpenClaw and CDP clients |
| Vulpine Mark | Public set-of-mark labeling for visual browser workflows |
| MobileBridge for Android | Public Android device discovery and session control |
| Vulpine API | Source-closed hosted extraction and browser workflow API |
| Vulpine Vault | Source-closed credential and authenticated-workflow surface |
| AudioBridge | Source-closed browser audio workflow surface |
| MobileBridge for iOS | Source-closed iOS device support |
Why VulpineOS Exists
Most browser-agent stacks still fail on three basic problems:
- Hidden prompt-injection content reaches the model.
- The page mutates between read and action.
- The model burns too much context on low-value browser structure.
VulpineOS handles those problems inside the browser/runtime itself:
| Layer | Purpose |
|---|---|
| Injection-Proof Filter | Removes hidden or non-visible content before it reaches the agent |
| Action Lock | Freezes the page while the agent is deciding |
| Optimized DOM Export | Compresses browser state into lower-token semantic output |
| Trust Warming | Builds stronger browser trust over time for long-lived identities |
Operator Stack
The runtime is not just a browser fork. It ships with the surfaces needed to run agents as an actual system:
| Surface | What it covers |
|---|---|
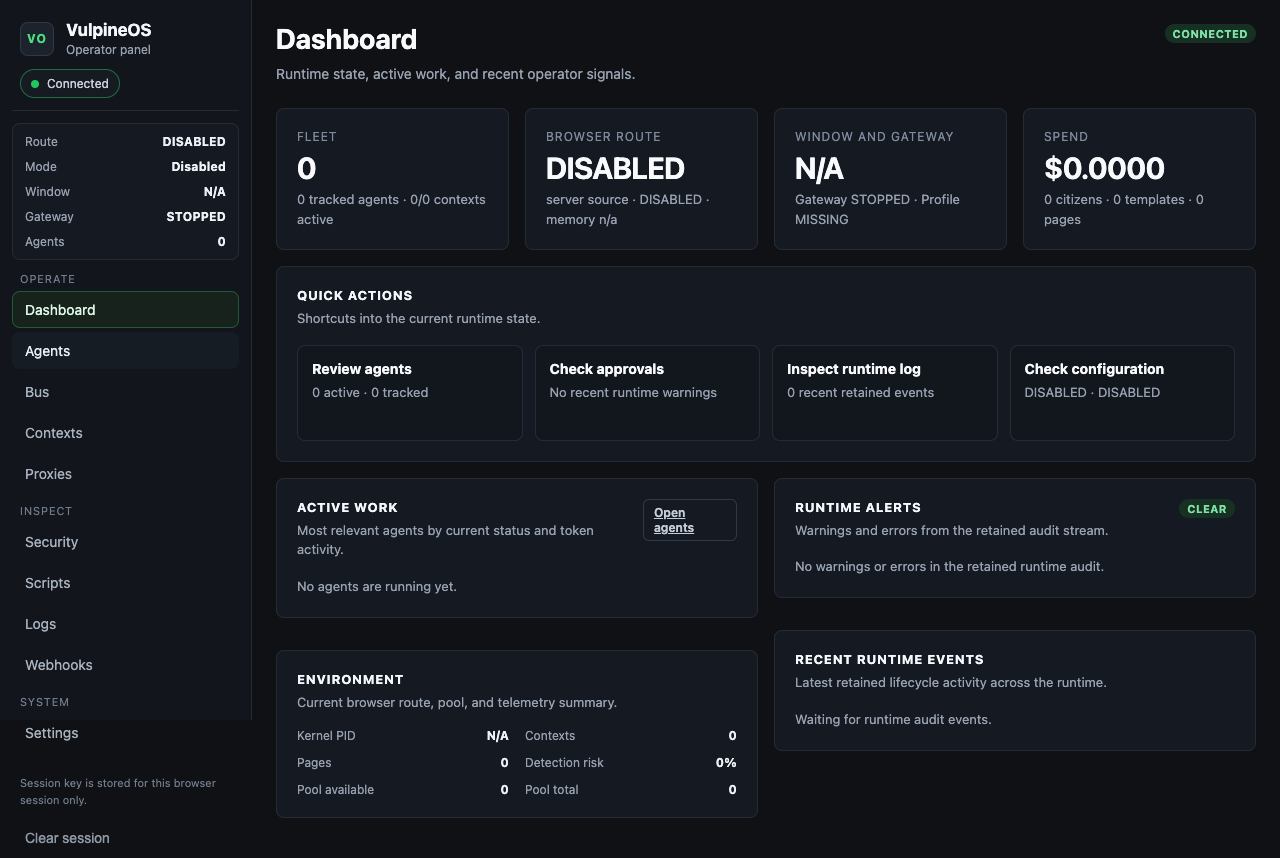
| Web Panel | Fleet view, agent sessions, approvals, proxies, contexts, logs, scripts, security, settings |
| TUI Workbench | SSH-friendly operator view with live conversations, contexts, and browser state |
| Remote Access | Remote TUI and remote panel control over the same runtime |
| MCP Browser Tools | 36 tools for browser control, reliability checks, realism, screenshots, audio, and mobile workflows |
| Foxbridge | CDP bridge so OpenClaw can drive the same Camoufox runtime |
Open Runtime, Commercial Surfaces
The runtime and tool interfaces are public. Some higher-level product surfaces remain source-closed.
| Open source | Source-closed |
|---|---|
| VulpineOS runtime | Vulpine API |
| Foxbridge | Vulpine Vault |
| Vulpine Mark | AudioBridge |
| Android MobileBridge | iOS MobileBridge |
The same public MCP and runtime interfaces can be present in both builds. Public builds return clear unavailable responses where a commercial provider is not attached. Commercial builds attach real providers behind the same surface.
See Source Availability for the exact boundary and Vulpine API Features for the hosted commercial surface.
Roadmap Direction
The next commercial product line currently centers on:
- Vulpine Sentinel — fleet stealth health monitoring
- Vulpine Replay — deterministic replay and audit bundles
- Vulpine Clockwork — mid-session identity rotation
The broader roadmap also includes Prism, Pulse, Forge, Scribe, Harbor, Mesh, and Oracle as later commercial products built around the same runtime.
Quick Start
git clone https://github.com/VulpineOS/VulpineOS.git
cd VulpineOS
make fetch
make setup
make dir
make build
./vulpineosUse ./vulpineos panel for the local operator panel, ./vulpineos tui for the terminal workbench, and ./vulpineos serve when you need a remote control plane.